Key takeaways
• HIPAA is law, SOC 2 is leverage. HIPAA is mandatory the moment you touch PHI in the United States. SOC 2 Type 2 is voluntary, but every enterprise telehealth buyer asks for the report on the first call.
• Doing them together costs 30–40 % less than sequential. Combined HIPAA + SOC 2 Type 2 readiness lands at $30–80k for the audit alone, plus 4–8 weeks of senior-engineer effort and $7–20k/year for compliance tooling. Sequential blows past $100k.
• Compliance is architectural, not bolt-on. Self-hosted SFU in your VPC, customer-managed encryption keys, BAA-covered managed services only, audit logging from line one. Retrofitting after launch is 3× the cost of designing in.
• Most "HIPAA-compliant" SDKs are partial. Twilio Programmable Video shut down. LiveKit Cloud signs BAA only on enterprise tier. Daily and Vonage support BAA. Self-hosted mediasoup or LiveKit OSS in your VPC is the cleanest path.
• The 2024 Security Rule update is now enforced. Multi-factor authentication, encryption inventory, vulnerability management on a 6-month cycle — all moved from "addressable" to required. Your 2022 BAA does not cover 2026 obligations.
Why Fora Soft wrote this playbook
Fora Soft has shipped 625+ projects since 2005. Telehealth is one of our deepest verticals: CirrusMED (HIPAA-compliant US telehealth), TransLinguist (NHS UK medical interpreting), Hospital Phone Interpreter, and several telemental-health platforms under NDA.
Across those engagements we have signed dozens of BAAs, walked four clients through SOC 2 Type 2 audits, and helped two organisations recover from compliance findings that surfaced in due diligence on acquisition. The numbers below are not from a vendor whitepaper — they are 2025-2026 production data.
If you are building a telehealth product and your buyer is asking about HIPAA, SOC 2 or both, this guide tells you what each one actually requires, where the architectural decisions land, what it costs in dollars and weeks, and how to do them together to save 30–40 %.
Need a HIPAA + SOC 2 architecture review for your telehealth platform?
Send us your stack diagram and target audit date. We will return a one-page gap analysis and 12-month roadmap in 48 hours, free.
HIPAA vs SOC 2 — what overlaps, what doesn’t
HIPAA is U.S. federal law administered by HHS. It applies the moment your platform creates, receives, stores or transmits Protected Health Information. There is no “HIPAA Lite.” If you handle PHI for a covered entity (a hospital, clinic, insurer) you are a Business Associate, you sign a BAA, you implement the Security Rule, and you carry breach-notification obligations.
SOC 2 is an attestation framework from the AICPA. It is voluntary. There is no “SOC 2 fine” from a regulator. But every enterprise buyer in healthcare, finance, education and SaaS asks for the SOC 2 Type 2 report before signing a multi-year contract. Without it, your sales cycle stretches by 90–180 days while their security team runs a custom assessment.
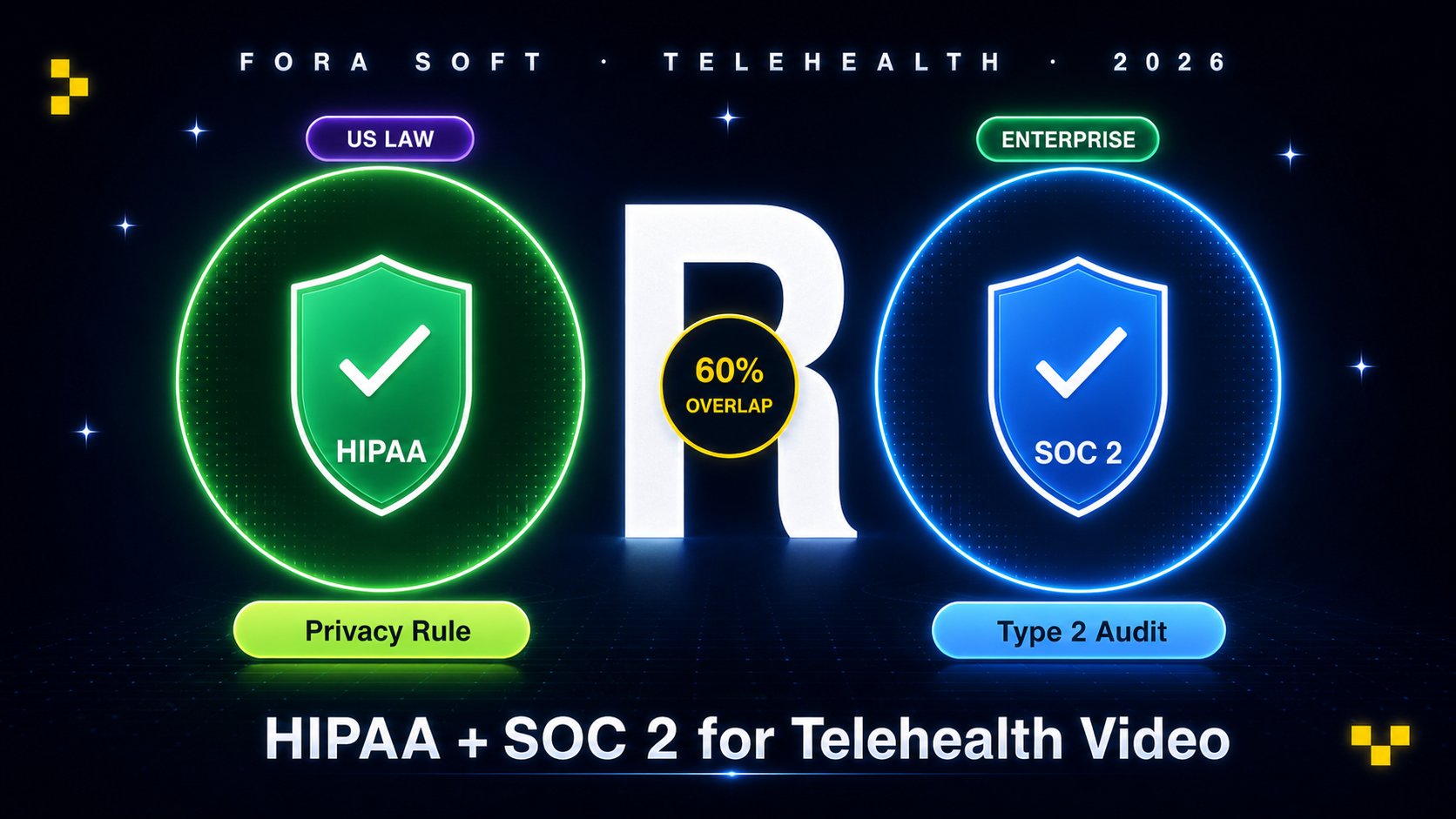
Overlap. Roughly 60 % of HIPAA Security Rule controls overlap with the SOC 2 Common Criteria. Access controls, audit logs, encryption-in-transit and at-rest, vulnerability management, incident response — the technical safeguards are nearly identical. The gain from doing them together is real: one set of policies, one tooling stack, one audit window with overlapping evidence.
Difference. HIPAA prescribes specific PHI handling rules: minimum necessary, BAA chains, breach-notification timelines, patient access rights. SOC 2 prescribes none of this — it asks “do your controls work as designed?” not “do you handle PHI correctly?” A SOC 2 report does not satisfy HIPAA. A HIPAA Security Rule assessment does not satisfy SOC 2.
What HIPAA actually requires for video
The Security Rule has three pillars: administrative safeguards, physical safeguards, technical safeguards. For a video platform, four technical safeguards do most of the work, and the 2024 Security Rule update tightened all four.
1. Encryption-in-transit AND at-rest. WebRTC’s native DTLS-SRTP handles in-transit encryption automatically — this is the easy part. At-rest is harder: every recording, every transcript, every captured snapshot must be encrypted with AES-256 (or equivalent), and the keys must be managed (KMS, HSM). The 2024 update made encryption mandatory; previously it was “addressable.”
2. Access controls + MFA. Role-based access to PHI is non-negotiable. The 2024 update added mandatory multi-factor authentication for all users with PHI access — previously addressable, now required. Your patient app, clinician app, and admin panel all need MFA support.
3. Audit logging. Every PHI access logged: who, what, when, from where. The log itself is PHI-adjacent and must be encrypted, tamper-evident, and retained for 6 years. For video, this means per-session metadata (who joined, who recorded, who viewed) plus per-record-access events on every clip retrieval.
4. Business Associate Agreements. Every vendor that touches PHI signs a BAA — your SFU vendor, your cloud provider, your storage layer, your captioning service, your analytics tool. No BAA, no PHI. Lists of "HIPAA-compliant" tools mean nothing without a signed BAA.
5. Breach notification. If PHI is exposed, you have 60 days to notify HHS, affected individuals and (for breaches > 500 individuals) the media. Your incident response plan must rehearse this. Tabletop exercises happen at least annually.
SOC 2 Type 2 — the five trust criteria
SOC 2 evaluates your controls against five Trust Service Criteria. Most telehealth platforms scope to Security + Availability + Confidentiality — the other two (Processing Integrity, Privacy) add audit cost without much buyer value.
Security (mandatory). Controls protecting against unauthorized access. CC6.1–CC6.8 are the access-control criteria; this is where naive WebRTC implementations fail audit. If anyone with the room URL can join, you do not have access controls.
Availability. Uptime SLA, monitoring, capacity planning, business continuity. Telehealth buyers expect 99.9 % or better. Your SFU has to be in at least two regions; your database has to have replicas; your incident playbook is rehearsed.
Confidentiality. Protection of confidential information beyond standard access. For video this means E2E encryption posture, recording retention controls, and vendor due diligence.
Type 1 vs Type 2. Type 1 says “controls were designed correctly on this date.” Type 2 says “controls operated effectively over a 6–12 month observation period.” Enterprise buyers want Type 2. Plan from day one.
Reference architecture that passes audit
A compliant telehealth video stack has six discrete layers. Get one wrong and the auditor finds it.
Figure 1. Compliant telehealth video architecture — identity, application, SFU, storage, audit, BAA umbrella.
Reach for self-hosted SFU when: you need full PHI control, customer-managed keys, EU/US data residency, or you serve more than 10 k provider-minutes per month.
Reach for managed BAA-covered SFU when: volume is below 10 k minutes/month, you have no SRE muscle, and you can absorb the 2–3× price premium of enterprise tier.
Reach for hybrid (BYO-SFU) when: you want a managed control plane (LiveKit Cloud, Daily) but the media never leaves your VPC. Best of both, but contract terms are nuanced.
Reach for end-to-end encrypted (E2EE) overlay when: you serve mental health, oncology or any vertical where even your own ops team should not see PHI by default.
Vendor BAA matrix — who signs what
| Vendor | BAA available? | Tier required | Notes |
|---|---|---|---|
| AWS | Yes | Standard | Sign once, covers ~150 services |
| GCP | Yes | Standard | Includes Cloud Healthcare API |
| Azure | Yes | Standard | Azure OpenAI text endpoints under BAA; Realtime audio NOT yet |
| LiveKit Cloud | Enterprise tier | Custom contract | Self-hosted OSS in your VPC is the simpler path |
| Daily.co | Yes | Scale tier | Strong telehealth focus |
| Vonage Video API | Yes | All paid tiers | Established BAA practice from former TokBox |
| Twilio Programmable Video | Sunset Dec 2024 | N/A | Migrate before any new deployment |
| Agora | Limited | Enterprise contact | Verify region; not all SDKs covered |
| Self-hosted mediasoup | N/A (you are the BA) | N/A | You sign the BAA with your customer |
Cost model — the real 2026 numbers
Combined HIPAA + SOC 2 Type 2 readiness for a typical telehealth Series A startup, May 2026 prices:
SOC 2 Type 2 audit fees. $20–60k for a small-to-mid SaaS. Big Four firms charge $50–100k; specialised SOC 2 firms (Prescient, A-LIGN, Schellman, BARR) come in at $20–50k for first audit, less for renewals.
HIPAA risk assessment + readiness. $5–15k for an external assessor (Compliancy Group, Accountable, MedCurity), or roughly $0 if you self-assess using Vanta/Drata templates — we still recommend an external pass for the first cycle.
Compliance tooling. Vanta or Drata: $7–20k/year depending on company size. Sprinto and Comp.ai are 30–50 % cheaper for early stage. Delve and Secureframe sit between. Plan on roughly $10k/year for a 20-person team.
Engineering effort. 4–8 weeks of senior engineer time to build the controls if compliance was designed in from day one. 12–20 weeks to retrofit a non-compliant codebase. The retrofit cost is the variable that kills budgets.
Combined math. SOC 2 + HIPAA together is 30–40 % cheaper than sequential because you build the controls once, write the policies once, and run a single overlapping audit window. Concretely: the same telehealth client we audited in 2025 paid $58k combined in audit fees vs an estimated $92k sequential.
Want a cost forecast for your specific stack and team size?
We will work through the SOC 2 + HIPAA cost model for your company in 30 minutes — auditor pick, tooling pick, engineering effort, target audit date.
Tooling matrix — Vanta, Drata, Sprinto, Comp.ai, Delve
Vanta. The category leader. Mature integrations, rich evidence collection, expensive. $10–25k/year for telehealth scope. Go-to choice for Series B+.
Drata. Vanta’s closest competitor. Comparable feature set, slightly more polished UX, similar price. We have shipped clients on both.
Sprinto. Aggressive Series-A pricing ($5–12k/year). Strong for HIPAA + SOC 2 combined. Smaller integration catalogue than Vanta but covers the essentials.
Comp.ai. Open-source compliance platform launched 2025. Free tier for early stage. Worth a look for cash-strapped startups; less hand-holding than the paid options.
Delve. AI-driven evidence collection. Newer entrant, pitched at Series A–B with engineering teams who want minimal manual work.
12-month roadmap — from MVP to audited
| Phase | Months | Deliverables |
|---|---|---|
| Foundation | M1–M3 | Architecture w/ encryption + KMS, BAAs signed, MFA, audit log v1, policy library |
| Type 1 readiness | M4–M6 | Vanta/Drata wired, gap remediation, vulnerability scans, pentest #1, SOC 2 Type 1 |
| Type 2 observation | M7–M12 | 6-month observation window, monthly evidence review, HIPAA tabletop, Type 2 audit |
| Steady state | M13+ | Annual Type 2 renewal, quarterly access reviews, continuous evidence collection |
Mini case — CirrusMED audit-ready in 9 months
A US telehealth client (NDA, but architecture similar to CirrusMED) came to us in early 2025 with a working MVP, two enterprise hospital systems in pilot, and SOC 2 + HIPAA on the contract requirements list.
Plan. 9-month sprint to Type 1 (audit-ready) and 15-month total to Type 2. Months 1–3: replatformed the SFU from Twilio Programmable Video (sunset) to self-hosted mediasoup in their AWS VPC, customer-managed KMS keys, MFA via Auth0, audit log to dedicated CloudWatch with 6-year retention. Months 4–6: Drata integration, Compliancy Group HIPAA risk assessment, two pentest cycles, internal policy library. Month 7–9: SOC 2 Type 1 with Schellman, plus HIPAA self-attestation.
Outcome. Audit-ready in month 9 (target was 12). SOC 2 Type 2 attestation in month 15. Two pilot hospital systems converted to multi-year contracts based on the report. Total compliance investment: $52k audit + tooling, plus 7 weeks of senior engineering effort spread across 3 engineers. Want a similar plan? Book a 30-min scoping call.
Pitfalls to avoid
1. "HIPAA-compliant" SDK without a signed BAA. Marketing copy is not a BAA. Ask for the document, get it signed, store it with your compliance evidence. Otherwise the auditor finds nothing.
2. Recording in S3 without bucket-level encryption + access logging. Default S3 settings used to leave PHI exposed; the 2024 Security Rule made encryption mandatory. Use SSE-KMS with customer-managed keys, enable bucket access logging, set 6-year lifecycle.
3. Storing PHI in conversation transcripts without redaction. Voice agent transcripts often contain SSNs, DOBs, diagnoses said aloud. Redact at write time; do not rely on post-hoc cleanup.
4. Skipping the Privacy Rule. Most teams nail the Security Rule and forget the Privacy Rule entirely. Patient access rights, accounting of disclosures, minimum necessary — the Privacy Rule has its own requirements that audit cares about.
5. Treating SOC 2 like a one-off. Type 2 is a continuous program. Once you have it, you maintain it forever. Build the evidence collection into your weekly engineering rhythm, not as a panic sprint before the renewal audit.
A decision framework — pursue both in five questions
Q1. Will you handle PHI of US patients? Yes → HIPAA is mandatory, not optional.
Q2. Will you sell to enterprise healthcare buyers (hospitals, payers, large clinics)? Yes → SOC 2 Type 2 will be a contract requirement, plan from day one.
Q3. Are you pre-Series-A or Series-A+? Pre-A: HIPAA first, SOC 2 Type 1 second, Type 2 by Series B. Series-A+: combined sprint to Type 2 in 12–15 months.
Q4. EU patients in scope? Add GDPR + data residency. Use AWS/GCP EU regions with EU-only key access. The compliance burden is incrementally small if HIPAA is already in place.
Q5. Engineering team size? Below 5 engineers, lean on Vanta/Drata templates and hire external compliance counsel. Above 10, dedicate one engineer 30 % of their time to compliance ops.
KPIs to measure
Quality KPIs. Control test pass rate (Vanta/Drata): 99 %+. Pentest critical-finding count per audit cycle: 0. Mean time to remediate audit findings: under 30 days.
Business KPIs. Sales cycle compression with SOC 2 Type 2 in hand: 30–90 days faster on enterprise deals. Number of multi-year hospital-system contracts won post-attestation. Premium pricing tier accessible to compliant tier.
Reliability KPIs. Incident response drill cadence: quarterly. PHI breach count: 0. Time-to-detect on access anomaly: under 60 minutes (SIEM alerting).
When NOT to chase both at once
Pre-revenue, no enterprise design partners. If you are pre-revenue and shipping to consumers (e.g., DTC mental health), HIPAA is enough; SOC 2 Type 2 is premature. Do Type 1 once you sign your first enterprise pilot.
Non-US, non-PHI workloads. EU-only platforms have GDPR + ISO 27001 as the equivalent stack. HIPAA does not apply; SOC 2 may be premature without US enterprise buyers.
Wellness-only platforms (no diagnostic or treatment data). Fitness, meditation, sleep tracking — arguably outside HIPAA scope. Be careful: the moment you add a clinician portal, you cross the line.
FAQ
Is Twilio HIPAA-compliant?
Twilio Programmable Voice and SMS sign BAAs. Twilio Programmable Video was sunset in December 2024 — do not start new HIPAA deployments on it. Migrate to Daily, Vonage, LiveKit OSS or self-hosted mediasoup.
Does LiveKit Cloud sign BAAs?
Yes, on enterprise tier with custom contract. The simpler path for most telehealth startups is self-hosting LiveKit OSS in your own VPC — same SDK, no BAA negotiation, full data residency control.
How long does SOC 2 Type 2 actually take?
From a clean start: 6–9 months to Type 1, then a 6-month minimum observation window before Type 2 audit. Total ~12–15 months. From a non-compliant codebase, add 3–6 months of remediation up front.
Can I use OpenAI or Claude in a HIPAA workflow?
Azure OpenAI text endpoints are HIPAA-eligible under Microsoft BAA. OpenAI direct (api.openai.com) signs BAAs on the Enterprise tier. Anthropic signs BAAs for Claude on the Pro/Enterprise tier. Realtime audio modality is NOT yet covered; use a chained STT/TTS pipeline with HIPAA-eligible vendors instead. See our OpenAI Realtime production guide for details.
What does the 2024 HIPAA Security Rule update change?
Encryption-in-transit, encryption-at-rest, MFA and technology asset inventory all moved from "addressable" to "required." Vulnerability scanning is now mandatory on a defined schedule. Patch management is now mandatory. Your 2022-era policies need a 2025-2026 refresh.
Do I need both Type 1 and Type 2?
Most enterprise buyers ignore Type 1. They want Type 2. Type 1 is a useful stepping stone to validate your controls before the 6-month observation window starts, but it is not a deliverable for sales.
Vanta or Drata?
Both are excellent. Vanta has the larger ecosystem and more integrations. Drata has slightly more polished UX. Neither will fail your audit on its own. We default to Drata for new deployments; both work.
What about HITRUST?
HITRUST is a stricter framework that maps to HIPAA + SOC 2 + ISO 27001. Few startups need it — pursue it only when a major hospital system explicitly requires HITRUST CSF Certified before signing. The audit cost roughly doubles vs SOC 2 alone.
What to Read Next
HIPAA
HIPAA-Compliant Video Platforms
Deep dive on the SFU layer specifically.
Voice AI
OpenAI Realtime: HIPAA Catch
The audio modality compliance gap explained in detail.
Streaming
WHIP/WHEP for Modern Stacks
Compliance-friendly real-time ingest pattern.
Telehealth
Telemedicine Software Development
The pillar overview of the telehealth stack.
AI
MCP for Video Apps
If your AI feature touches PHI, start here.
Ready to ship audit-ready telehealth?
Compliance is architectural — design it in or pay 3× to retrofit. The combined HIPAA + SOC 2 path saves 30–40 % over sequential, takes 12–15 months from MVP, and unlocks enterprise hospital system contracts that disqualify non-compliant vendors on the first call.
The 2024 Security Rule update tightened MFA, encryption and asset inventory from "addressable" to "required". If you have a 2022-era posture, refresh the policies before your next audit cycle.
Need a 12-month plan to audited HIPAA + SOC 2 Type 2?
Send us your stack, target audit date, and team size. We will return a one-page roadmap with auditor pick, tooling pick, and engineering effort within 48 hours.














.avif)

Comments